You are seeing a free-to-access but limited selection of the activity Altmetric has collected about this research output.
Click here to find out more.
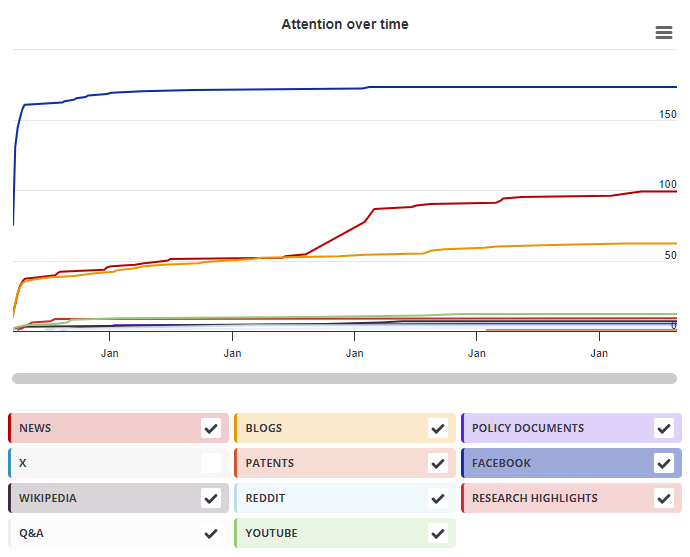
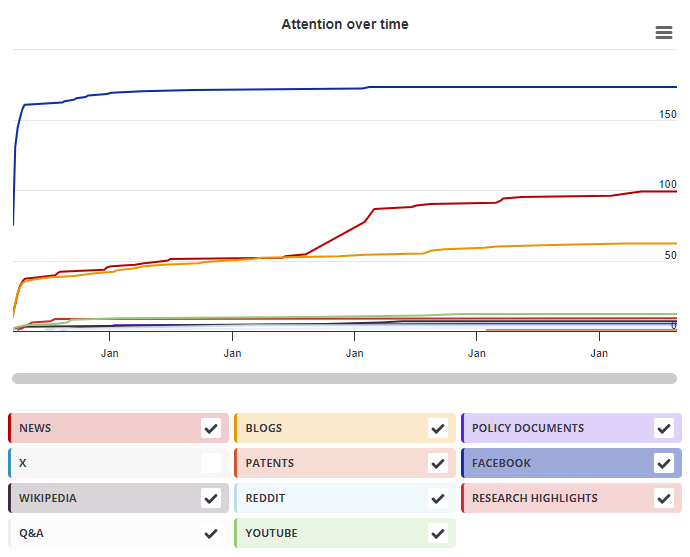
Timeline
Mendeley readers
| Chapter title |
Efficient Set Operations in the Presence of Malicious Adversaries
|
|---|---|
| Chapter number | 19 |
| Book title |
Public Key Cryptography – PKC 2010
|
| Published by |
Springer, Berlin, Heidelberg, May 2010
|
| DOI | 10.1007/978-3-642-13013-7_19 |
| Book ISBNs |
978-3-64-213012-0, 978-3-64-213013-7
|
| Authors |
Carmit Hazay, Kobbi Nissim |
Mendeley readers
The data shown below were compiled from readership statistics for 32 Mendeley readers of this research output. Click here to see the associated Mendeley record.
Geographical breakdown
| Country | Count | As % |
|---|---|---|
| Malaysia | 1 | 3% |
| Unknown | 31 | 97% |
Demographic breakdown
| Readers by professional status | Count | As % |
|---|---|---|
| Student > Ph. D. Student | 11 | 34% |
| Student > Master | 7 | 22% |
| Lecturer | 2 | 6% |
| Researcher | 2 | 6% |
| Student > Postgraduate | 2 | 6% |
| Other | 5 | 16% |
| Unknown | 3 | 9% |
| Readers by discipline | Count | As % |
|---|---|---|
| Computer Science | 22 | 69% |
| Physics and Astronomy | 2 | 6% |
| Agricultural and Biological Sciences | 1 | 3% |
| Mathematics | 1 | 3% |
| Engineering | 1 | 3% |
| Other | 1 | 3% |
| Unknown | 4 | 13% |